Do you want to be part of the community?
Do you want the best professionals?
Advantages
The opportunity to optimize your cybersecurity with epic bounties.
Optimise
your budget
It will only consume budget by adding new identified vulnerabilities identified.
Allows to adjust
times
By regulating the number of participating researchers, the search can be accelerated to the maximum.
Vulnerabilities
customised
Select vulnerabilities in a fully customisable way and real vulnerabilities.
Real time results
Select vulnerabilities in a fully customized way.
How it Works?
1. The companies publish their programs
The assets that companies need to protect will be published from their private platform. from its private platform. The company will have a streamlined process optimised process, which will make it possible to facilitate and delimit the programme according to their needs in a comprehensive manner.
2. The hunters experts will look for vulnerabilities
The programme will be accessible to the expert community best suited to the needs of the programme. best suited to the needs of the programme. The best hunters in each will provide their expertise in the search for vulnerabilities in the asset. asset.
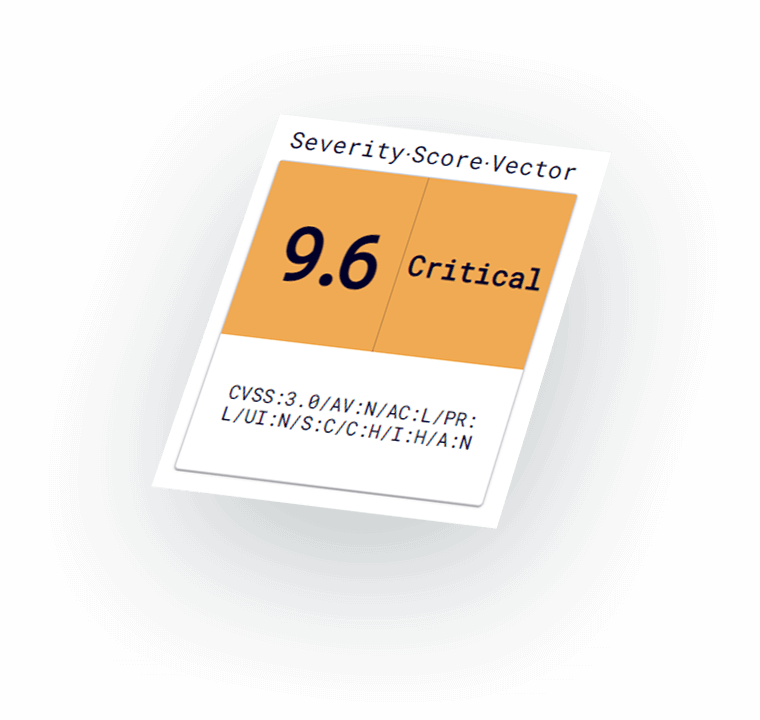
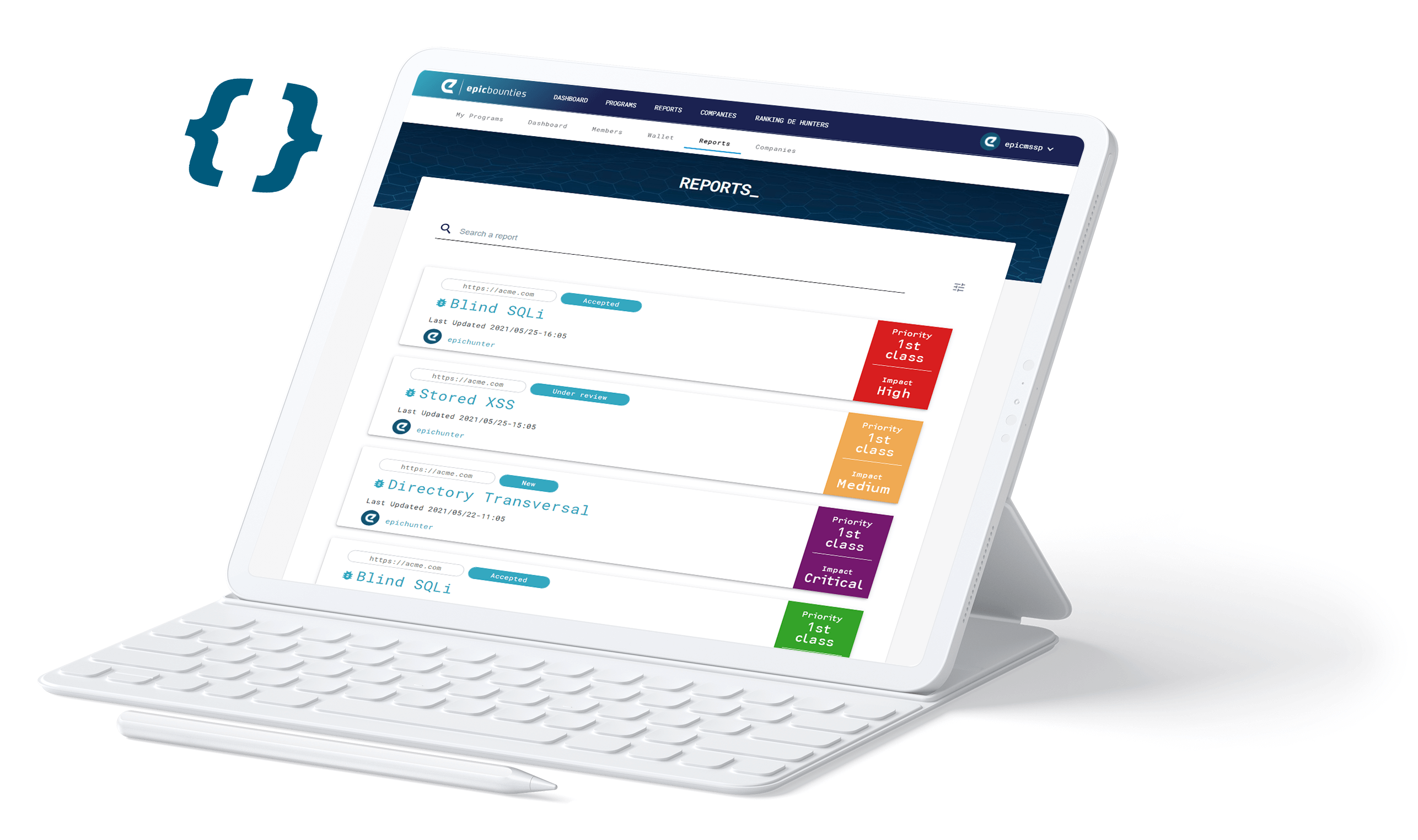
3. It generates an appropriate report for the company
Each time a vulnerability is found, it is reported through the platform in professional the platform as a professional report for verification. The platform itself facilitates this process in order to guarantee the highest quality of the results delivered.
4. The hunter is rewarded for every vulnerability found
If the vulnerability exists and has been validated with the requirements of the the hunter receives the corresponding reward for his work. work. In this way the company only pays for the vulnerabilities found, and the hunter is rewarded according to the success of his appropriate to the success of his participation in the programme.
Our team
Articles about Bug Bounty

Epic Bounties recognized as the best project of the Keiretsu Investors Forum.
Málaga, Spain, Febrary 2023. Epic Bounties recognition as the best project.
Read more
From Pentesting to Pentesting as a Service (PaaS)
Málaga, Spain, Decemeber 2022. From Pentesting to Pentesting as a Service (PaaS) Pentesting (al...
Read more
ICA Sistemas y Seguridad and Epic band together for making customers systems’ safer
Málaga, Spain, July 2022. As part of our expansion plan we just signed a new partnership agreeme...
Read more
Two bigs of security are joining forces
Málaga, Spain, June 2022. Two bigs of security are joining forces. SMARTFENSE has launched a bug...
Read more
Contact